SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact Us
Apply your credits to renew your certifications
Attend a live, instructor-led class at a location near you or remotely, or train on your time over 4 months
Course material is geared for cyber security professionals with hands-on experience
Apply what you learn with hands-on exercises and labs
Gain essential technical and leadership skills to effectively manage security programs, covering key topics like security architecture, vulnerability management, cloud security, and GenAI security.
This is an excellent primer for management types. I come from a technical background and can see the value there plain as day.
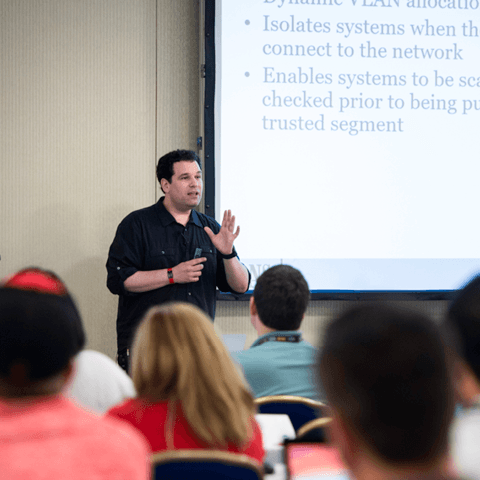
LDR512 is security manager training that equips security leaders with the technical and leadership skills needed to manage security programs, covering essential topics like frameworks, vulnerability management, and cloud security. As a foundational cyber security management course, it also prepares professionals for the GSLC certification (GIAC Security Leadership Certification). Through hands-on Cyber42 simulations, participants build real-world skills for developing effective security teams and managing information risk.


SANS Fellow Frank Kim helps to develop the next generation of CISOs and cyber leaders while teaching LDR512 and LDR514.
Read more about Frank KimExplore the course syllabus below to view the full range of topics covered in LDR512: Security Leadership Essentials for Managers.
This section introduces essential knowledge for security leaders, covering cybersecurity frameworks, risk management, policy development, and team structure to support effective security program management.
This section covers traditional and modern security architectures, focusing on network security, endpoint controls, cloud security with AWS, IAM risks, and the Zero Trust Model to address evolving security challenges.
Section three covers security engineering best practices, including cryptography, privacy concepts, application security with DevSecOps, Infrastructure as Code (IaC), and securing generative AI (GenAI) and Large Language Models (LLMs).
This section equips managers to lead security initiatives, covering vulnerability management, security awareness, vendor negotiation, and effective project execution to foster a security-aware culture and drive project success.
Section five focuses on detection and response, covering SIEM and SOC functions, incident response, business continuity, disaster recovery, and physical security controls for comprehensive security operations management.
Lead cybersecurity risk strategy at the highest level.
Explore learning pathLeads privacy program development and compliance oversight to ensure adherence to privacy laws, standards, and executive data protection needs.
Explore learning pathOversees a portfolio of IT capabilities aligned to enterprise goals, prioritizing needs, solutions, and value delivery to the organization.
Explore learning pathResponsible for overseeing and directly managing technology projects. Ensures cybersecurity is built into projects to protect the organization’s critical infrastructure and assets, reduce risk, and meet organizational goals. Tracks and communicates project status and demonstrates project value to the organization.
Explore learning pathDaily focus is on the leadership of technical teams. Includes titles such as Manager, Information Security Specialist, and Program/Project Leader.
Explore learning pathResponsible for managing the cybersecurity of a program, organization, system, or enclave.
Explore learning pathResponsible for managing the Communications Security (COMSEC) resources of an organization.
Explore learning pathDesigns and evaluates information system security throughout the software lifecycle to ensure confidentiality, integrity, and availability.
Explore learning pathAdd a GIAC certification attempt and receive free two practice tests. View pricing in the info icons below.
This course continues to challenge and develop leadership capabilities to better prepare individuals to help their organizations thrive within the cyberspace.
The content makes us truly understand why and what we should be doing as a cybersecurity leader.
For a Security Manager, this class is spot on!
Cyber42 was an amazing game and experience. Not only building connection with our peers, but also creating a rich dialogue. More importantly, the sharing and decision analysis really helped us learn the materials more effectively.
Get feedback from the world’s best cybersecurity experts and instructors

Choose how you want to learn - online, on demand, or at our live in-person training events

Get access to our range of industry-leading courses and resources