SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsIT and ICS/OT fulfill distinct purposes, pursue different objectives, and manifest diverse consequences in case of an incident.


With my firm ICS Defense Force, I perform industrial control system (ICS) security assessments, incident response tasks, and incident response tabletop exercises across multiple critical infrastructure sectors, globally. I’ve recently conducted these projects in the European energy sector. It is important to describe my practical fieldwork in this context. It allows me to meet with security teams, engineering staff, and those leading the charge of cybersecurity risk management and defense for critical infrastructure. This includes connecting with the decision-makers who are seeking technical solutions and tactical ICS-specific training to address their identified cybersecurity challenges.
In recent years, the realm of ICS/Operational Technology (OT) cybersecurity has become a focal point in the ongoing battle against cyber threats. This has been the case observed in specific targeted cyber-only ICS attacks, but also attacks on ICSs seen as part of overall warfare and larger geopolitical conflicts. The increasing integration of digital technologies into critical infrastructure has exposed industrial systems to a myriad of sophisticated and advanced persistent threats. Numerous high-profile case studies underscore the severity of the situation, revealing the targeting and impact of industrial cyber security incidents.
For example, ransomware targeting sectors within the European region is also accelerating. According to the ENISA’s 2023 Threat Landscape report, the top ransomware threat groups are targeting industrial and manufacturing sectors. In these instances, causing disruptions to manufacturing operations or taking command of industrial systems can lead to considerable financial setbacks, operational downtime, and possible safety concerns, rendering them appealing target by adversaries. It appears today that threat groups primarily target United States organizations with ransomware. However, Germany, France, Spain, and Austria remain in the top 10 regions targeted with Blackcat and Lockbit ransomware.
Beyond ransomware, specific targeted ICS attacks on critical infrastructure still ring true today. In December 2015, Ukraine experienced a significant cyber-attack targeting its power grid. Using the "BlackEnergy" malware for initial access into an IT network, remote access to power HMIs (human-machine interfaces), as well as "KillDisk" malware components and other coordinated efforts, attackers disrupted the industrial control systems at over 60 substations. The attack resulted in a widespread power outage, leaving around 225,000 people without electricity for several hours. A year later in 2016, a Ukraine transmission-level substation was compromised using a new malware framework dedicated to power systems attacks abusing the IEC-104 protocol with the CRASHOVERRIDE ICS malware. These ICS incidents underscore the targeting of critical infrastructure in the region.
However, regardless of sector or region, threats to ICS/OT infrastructure globally have expanded with the discovery of PIPEDREAM. PIPEDREAM/Incontroller is a scalable ICS-specific attack framework which can be deployed for disruptive and possibly physically destructive impacts to operations and safety across any ICS infrastructure. PIPEDREAM allows adversaries to live off the land more easily. The framework can impact a wide variety of vendor PLCs and abuse already installed legitimate industrial automation software. Also, PIPEDREAM allows attackers to abuse legitimate ICS network protocols within the ICS environment, including but not limited to OPC-UA, Modbus, and some proprietary control protocols. This fortifies the need for specifically trained ICS cybersecurity analysts and ICS/OT risk managers defending the industrial control system space.
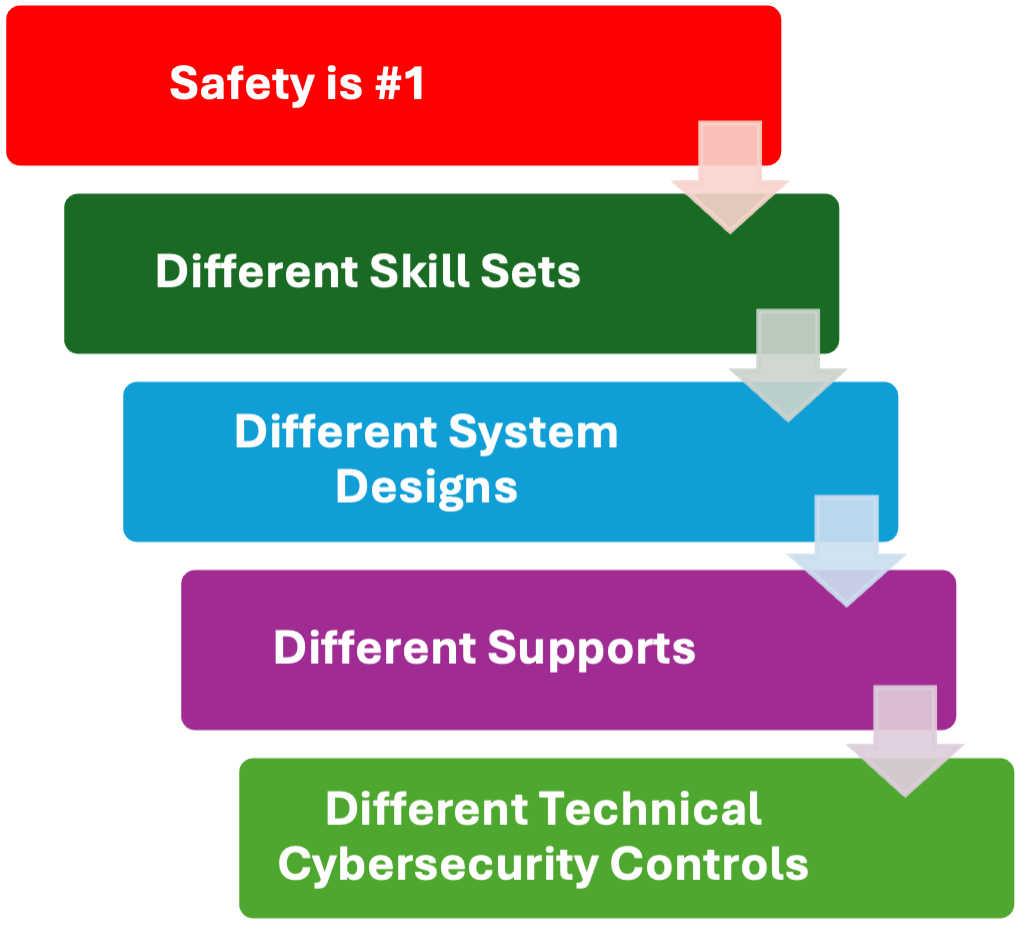
Drawing parallels between industrial engineering control system assets and conventional IT assets can often be misleading. IT and ICS/OT fulfill distinct purposes, pursue different objectives, and manifest diverse consequences in case of an incident. Additionally, ICS systems comprise a range of devices, including embedded operating systems and engineering devices employing unconventional industrial protocols not found in traditional office settings that IT staff are experienced in securing. Many pieces of engineering hardware equipment are proprietary and do not operate on conventional operating systems. While there are many differences between IT and ICS and operational environments, the primary technical differences between IT and ICS exist in these main areas, including cybersecurity controls:
When adversaries target ICS environments, they typically utilize specific attack tactics and techniques to gain access and execute their attacks, aiming to compromise control systems and have an impact in the physical world. The range of attacks on ICS environments varies, encompassing the manipulation and physical control of an engineering process, abuse of existing systems (ICS living off the land attacks), downtime, and the potential for safety consequences such as injury or death, including direct damage to physical engineering equipment and property.
Directly transferring traditional IT security controls into an ICS environment can create a misleading sense of security and introduce unforeseen and potentially disastrous consequences that may jeopardize the safety of individuals and engineering equipment. For example, this aligns with Department of Homeland Security (DHS) when IT security controls and processes are put in place inside of a control system, “Standard cyber incident remediation actions deployed in IT business systems may result in ineffective and even disastrous results when applied to ICS cyber incidents, if prior thought and planning specific to operational ICS is not done.”
Specific ICS training and specific ICS cybersecurity critical controls are required to protect our targeted critical infrastructure.
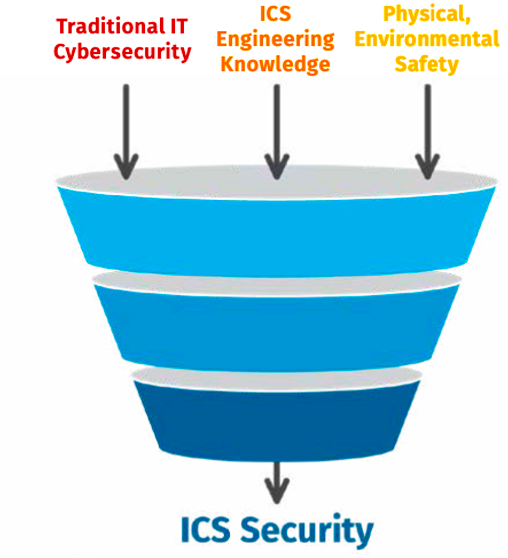
Mature cybersecurity professionals specializing in ICS cybersecurity recognize the distinctions between conventional IT and ICS/OT security. As leaders in ICS risk management strive to cultivate their security teams, it is imperative they consider the specific skill set requirements essential for effective ICS cybersecurity. To ensure the team's proficiency and safety to operations, those responsible for ICS/OT cybersecurity will do well to recruit, train, and retain their teams with a combination of the following key skills:
Traditional IT Cybersecurity + Basic Engineering Knowledge + A Prioritization of Physical Safety at Their Facilities = Proficiency in Operational Safety.
ICS418: ICS Security Essentials for Managers
Cybersecurity leaders in the European regions are aware that the primary layer in the comprehensive defense-in-depth approach for ICS and OT environments consists of policies, procedures, and awareness. In this context, specific awareness related to ICS emphasizes fostering a culture of cybersecurity consciousness among operators, engineers, IT staff, and facility stakeholders, placing safety as the top priority. The importance of ICS security awareness to roles that support and directly work in ICS, with the prioritization of safety, cannot be emphasized enough, given their pivotal role in safeguarding critical infrastructure. ICS-specific cybersecurity awareness training serves as the cornerstone of an effective defense-in-depth strategy for the protection of critical infrastructure. Leaders responsible for ICS cybersecurity are expected to align with safety and deploy ICS specific awareness as part of the overall ICS cybersecurity program moving forward. Such alignment enhances resilience against a spectrum of risks, addressing not only physical accidents but also the evolving digital threats in industrial settings, all while maintaining a steadfast commitment to prioritizing the safety of individuals.
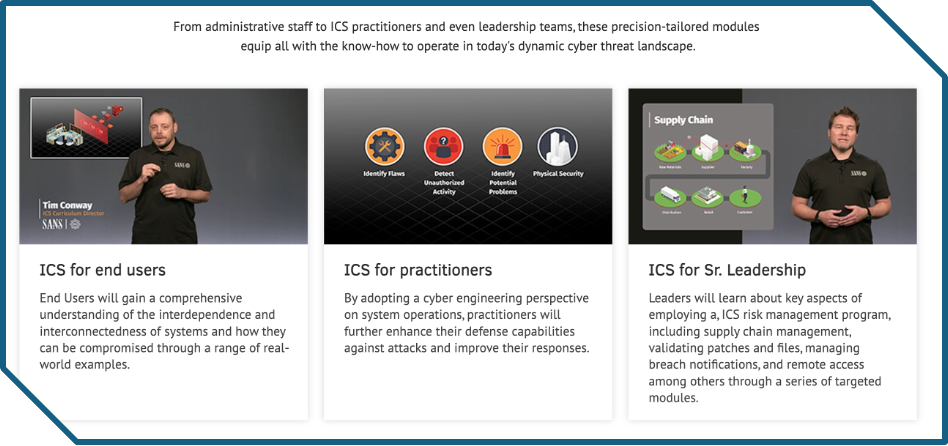
Training and development opportunity for ICS Security Analysts, IT Security Staff, ICS Security Architects, ICS Security Incident Responders, and Process Control Engineering staff:
The SANS ICS410: ICS/SCADA Security Essentials course establishes technical knowledge and understanding across a diverse set of professionals who engineer or support control systems and share responsibility for the security in ICS environments including the power grid sector.
Training and development opportunity for ICS Security Architects, IT Security Staff, ICS Security Incident Responders, and Process Control Engineering staff:
The SANS ICS515: ICS Visibility, Detection, and Response course meets several modern ICS security challenges with practical techniques and applied knowledge for effective ICS security to protect critical infrastructure. ICS515 teaches students how to perform tactical ICS incident response by leveraging hands-on labs. Labs include assembling, running, and troubleshooting a programmable logic controller (PLC) like you’d see in an electric power utility – including the generation, transmission, distribution, and intertie operations. Students keep the power grid PLC kit for continued learning after class is over. Students from IT, ICS, and engineering will detect and defend against threats in several realistic power grid attack scenarios.
Training and development opportunity for ICS Security Architects, ICS Security Incident Responders, and Process Control Engineering staff:
The SANS ICS612: ICS Cybersecurity In-Depth course is an in-classroom lab setup that moves students through a variety of exercises demonstrating how an adversary can attack a poorly architected ICS environment and how ICS-trained defenders can secure and manage the environment. Representative of a real ICS environment, the classroom setup includes a connection to the enterprise, allowing for data transfer, (i.e., Historian), remote access, and other typical corporate functions to understand, maintain, and defend.
In conclusion, on behalf of myself and the SANS ICS team, I would like to say thank you for taking the time to read this blog, as the tactical ICS/OT cybersecurity protection of critical systems in the European region is such an important topic. For practical hands-on ICS/OT cybersecurity training and the in-person ICS Summit, join us in Munich at the ICS Europe Summit & Training event, 12-18 May 2024, and help defend your ICS and critical infrastructure!
Be safe from industrial cyber incidents!
- Dean


Dean Parsons, CEO of ICS Defense Force, teaches ICS515 and co-authors ICS418, emphasizing ICS-specific detection, incident response, and security programs that support OT operations—aligning practitioners and leaders on clear, defensible action.
Read more about Dean Parsons