SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsSecurity Operations Center Ill-Equipped and Unprepared

This is Part 3 of 4-part series. Read the other parts here:
Rekt Casino (a fictional organization) has learned some hard lessons following a major ransomware incident and data breach, but it’s on the slow road to recovery and improvement. In Part 1 and Part 2 of our Operational Leadership blog series, we talked about using the Center for Internet Security (CIS) controls to establish a basic set of controls, and implementing continuous vulnerability assessment (CIS control #3) to measure and address weaknesses in the environment. In this post, we’ll discuss Rekt’s next priority: upgrading its security team from three IT staffers to a dedicated security operations center (SOC).
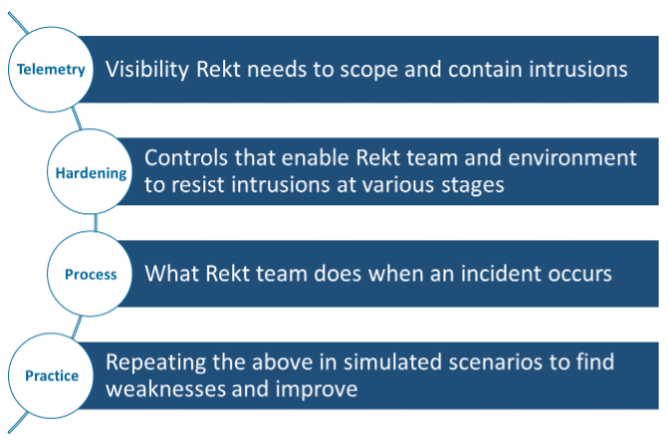
SOC telemetry starts with monitoring at the network and host layers and will ultimately extend to Rekt applications and user identity. Looking back at the recent incident, we can see that there are many stages of the attack that could have been disrupted or detection given the right visibility. In a “green field” environment like the Rekt network, we should focus on identifying the most damaging stages of an attack first – namely data destruction or exfiltration. Once we have reduced our exposure and improved our detections for these activities, we can move to earlier stages like initial exploitation and delivery.
Preparing the environment to resist future attacks and support a detection-oriented defense is not something our newly-minted SOC can do alone. Fortunately, this process has already begun in Parts 1 and 2 of our series. The insights we will gain from our first CIS controls and our new vulnerability assessment program will give our SOC the context it needs to discern legitimate activities from suspicious ones.
We can combine these external inputs and internal inputs to produce a rudimentary threat model. This model will help us narrow down the adversaries (or types of adversaries) who are most likely to target Rekt Casino. Doing some additional homework can tease out details of what specific tactics and techniques those adversaries are likely to use. And our vulnerability assessment reporting can tell us where our weaknesses might increase those adversaries’ likelihood of success. Now the SOC has a clear roadmap that indicates where investment is needed from a detection and controls standpoint.
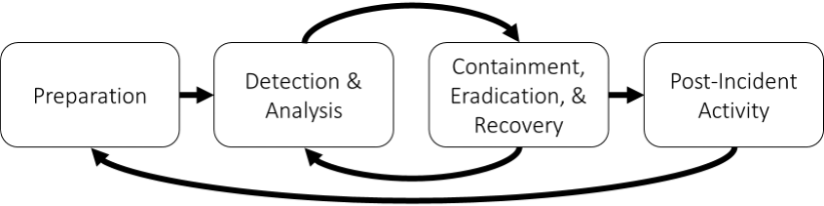
In the first SANS Leadership series on the Rekt Casino breach, we talked about how Rekt’s lack of business focus on security contributed to poor detection and response capabilities. Building these capabilities from the ground up requires a renewed focus on security at the leadership level expressed in the form of security policies: what is allowed in the environment? How can Rekt IT assets be used responsibly? These policies inform our incident response plans: what happens when Rekt IT assets are abused, misused, or exploited? In turn, these plans inform processes that the SOC will execute in the event of an incident. Processes may come in the form of playbooks, operating procedures, or automated workflows. These operational elements of the response process will happen primarily between the Detection and Containment phases, with other teams participating in various capacities throughout the process.
Another key input to the SOC will be our understanding of our adversaries, what they are after, and how they are likely to get it. The recent breach and the knowledge that other casinos have suffered similar attacks gives us valuable insights into future activity. Now the question is, how do we convert that intelligence to better detections and other defensive capabilities? Reference frameworks like MITRE’s ATT&CK Matrix, which enumerates common offensive tactics and techniques, can help us put our knowledge of the attacker into context of what we might see in our environment. Identifying and prioritizing TTPs based on what we have seen internally and what we know has happened to other organizations in Rekt’s industry can help us prioritize defenses, write new detections, and hunt for evidence that we may not have identified through automated alerting. This prioritized approach is critical for an organization like Rekt, where there is obviously so much to do but limited time and resources to do it.

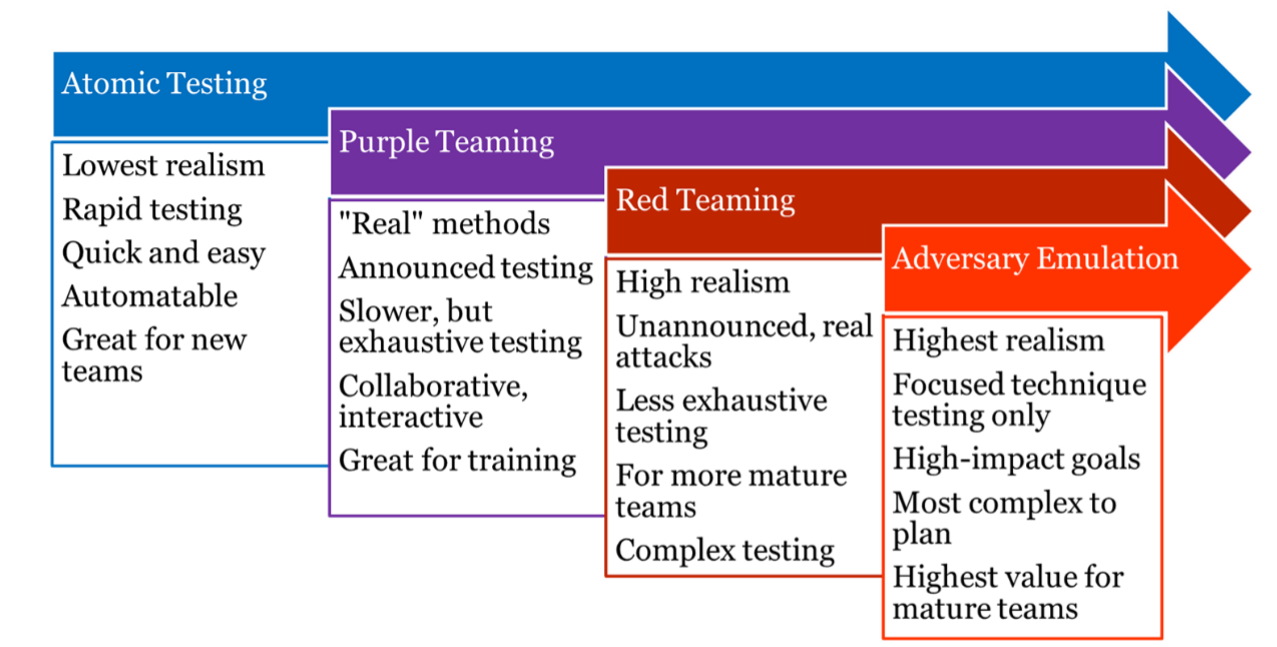
Given the amount of investment the SOC will require, Rekt Casino’s leadership understandably wants to be certain their new defenses are working as intended and are measurably improving over time. This can be a difficult thing to measure, especially when incident activity tends to happen on an inconsistent timeline. Continuous testing and validation is a great way to prove out our new SOC capabilities so that we can be confident in our ability to detect the next incident before it actually happens. Think of this testing as a continuum where we can conduct isolated “unit tests” for new detections we might create on one end, and full-featured adversary simulations to put our entire security program to the test. For an immature security program such as the one Rekt Casino currently has, atomic testing and purple teaming are probably the most appropriate. These introduce an element of realism while being focused on transparency and collaboration.
Building and leading SOC teams is a complex, multi-discipline process. But by focusing on a few key goals and basic capabilities we can break the challenge down into more manageable elements that we can improve and refine. Incorporating threat intelligence and information about our own environment, driven largely by our controls, weaknesses, and visibility, can help us prioritize these elements and ensure our SOC tools and processes are tailored to Rekt Casino’s unique business and threat model.
Mark Orlando is a SANS Associate Instructor, co-author of LDR551: Building and Leading Security Operations Centers, instructor for SEC450: Blue Team Fundamentals: Security Operations and Analysis, and the Co-Founder and CEO of Bionic Cyber. Prior to Bionic, Mark built, assessed, and managed security teams at the Pentagon, the White House, the Department of Energy, and numerous Fortune 500 clients. Mark has presented on security operations and assessment at DefCon's Blue Team Village, the Institute for Applied Network Security (IANS) Forum, BSidesDC, and the RSA Conference and has been quoted in the New York Times, the Washington Post, Forbes, and many other publications. He holds a Bachelor's Degree in Advanced Information Technology from George Mason University and served in the US Marine Corps as an Artillery Non-Commissioned Officer. Read Mark's full profile here.


Mark Orlando brings extensive cybersecurity leadership experience from the Pentagon, White House, and Fortune 500 sectors. As Bionic Cyber's CEO, he's a respected security operations expert with military and academic credentials.
Read more about Mark Orlando