SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
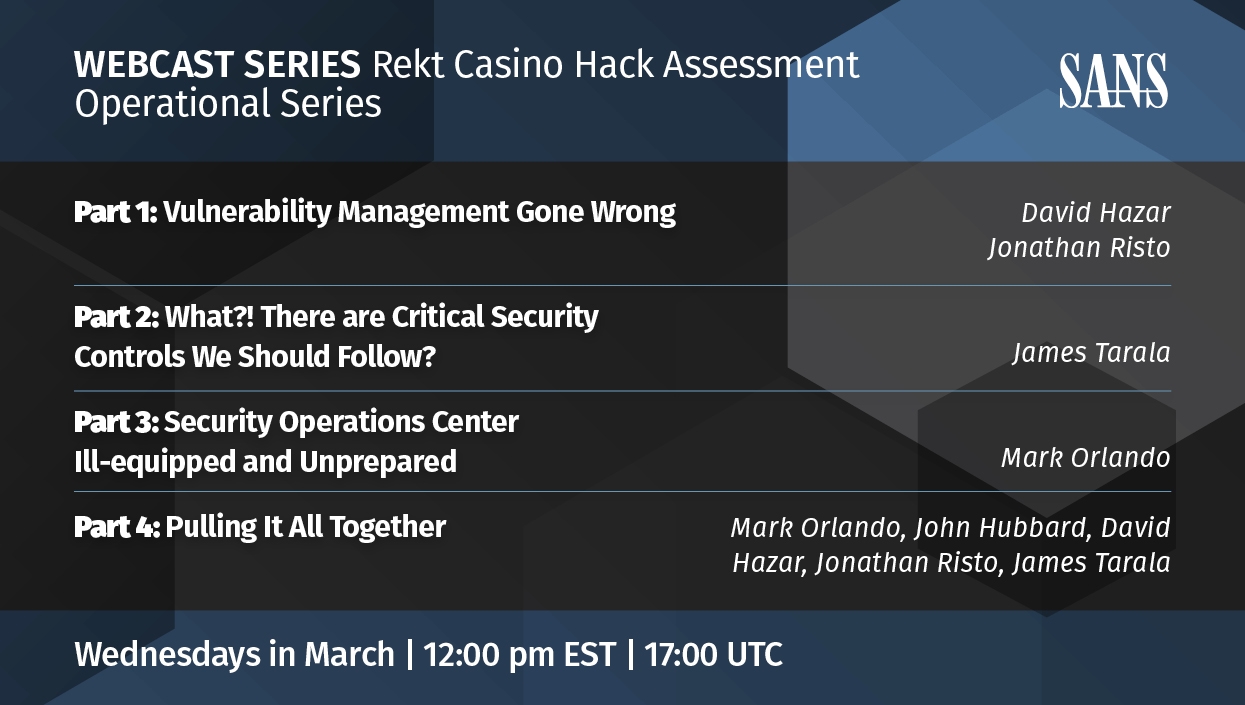
Contact UsRekt Casino Wrap Up: A Transformation Cybersecurity Leader Perspective

This is Part 4 of 4. Read the other parts here:
If you haven’t been following the Rekt Casino webcast series, I’ll give a quick summary: Rekt Casino suffered a breach due to a ransomware attack. Rekt Casino did not have an operationalized security program that had a framework, policies, technologies, or administrative controls to ensure the security of their systems and data.
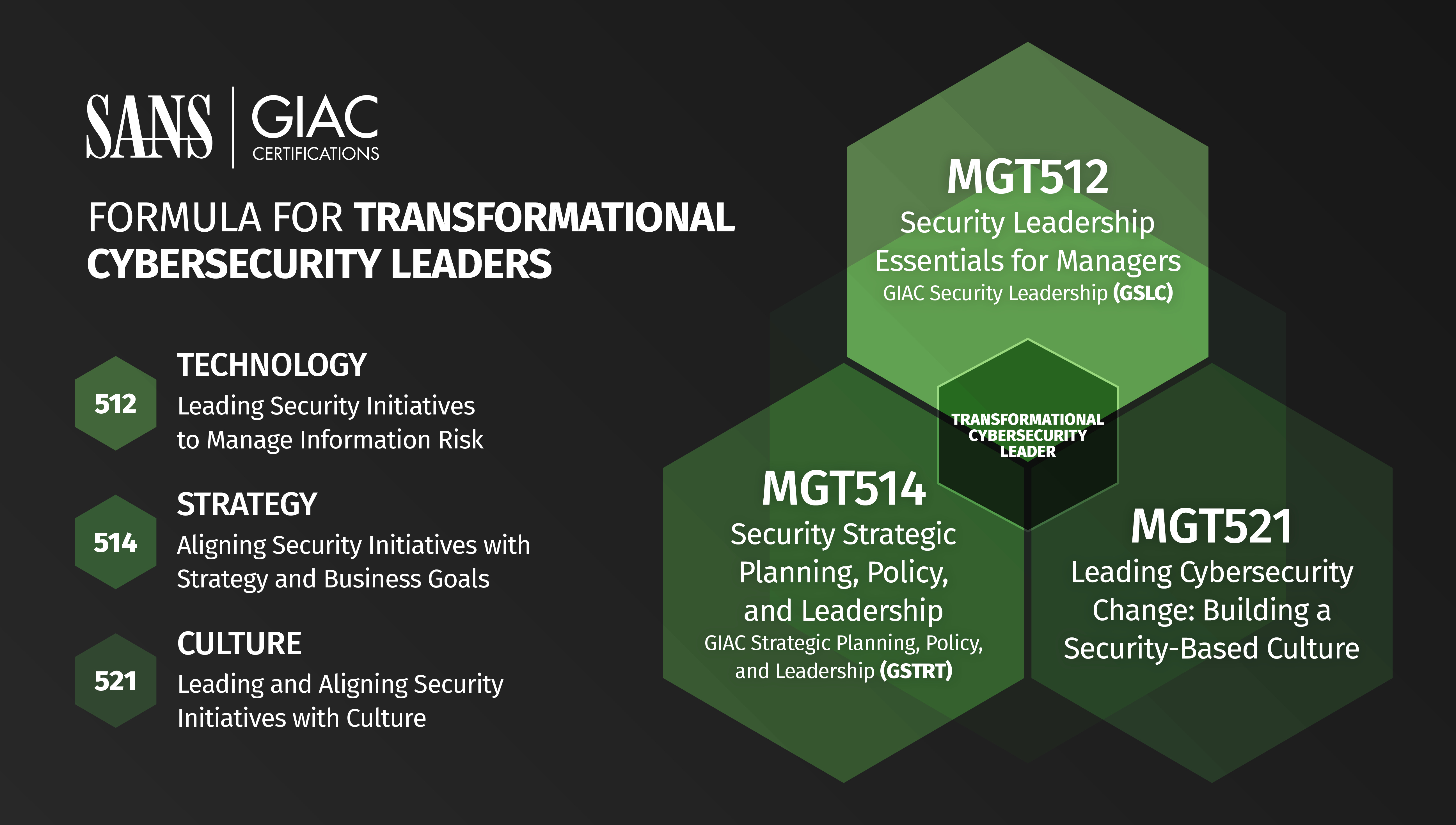
We then took a look at the breach from the perspective of the three different courses that make up the Transformational Security Leader Triad:
MGT512: Security Leadership Essentials for Managers with Kevin Garvey,
MGT514: Security Strategic Planning, Policy, and Leadership with Joe Sullivan, and
MGT521: Leading Cybersecurity Change: Building a Security-Based Culture with Lance Spitzner and Russell Eubanks.
If you look at each of these perspectives, what becomes evident is that you need a well-rounded skill set in today’s modern organizations to lead the business of security. The reason for that is security is no longer an IT issue, it’s an enterprise risk management issue.
To manage security and risk from an enterprise level perspective takes an understanding of the strategic planning and alignment, the technologies involved, and understanding how to lead change and build a security aware culture. As you progress through the Transformational Cybersecurity Leader Triad, you acquire the knowledge for these three key leadership perspectives.
Looking back at Rekt Casino, let’s consider what it would have looked like from a Transformational Cybersecurity Leader Triad perspective from a high level.
MGT512: Security Leadership Essentials for Managers would have provided the team with an understanding of:
That would have provided the team with a strong technical foundation, but in order to strategically align security with the strategic business objectives the team needs to have an understanding of strategic planning and leadership.
MGT514: Security Strategic Planning, Policy, and Leadership would complement the technical understanding of MGT512 from a high level with and understanding of:
At this point the team has operationalized security from an enterprise risk management perspective, but all the work, analysis, and planning to this point means there’s going to be a lot of changes at Rekt Casino. Rekt Casino had no formal security program in the beginning and that means there was no security awareness or security culture within the organization.
There’s an art and science to leading change and developing culture as you deliver on your strategic plan for security. You need an understanding and a plan for leading change in your organization, and that’s where MGT521 compliments both MGT512 and MGT514.
MGT521: Leading Cybersecurity Change: Building a Security-Based Culture at a high level enables the team to understand:
The outcome of this change is an organization with a much stronger security culture that aligns with and supports the organization’s overall culture. As a result, not only will the workforce be far more secure, but the organization’s security initiatives as defined from MGT512 will be far more likely to succeed.
Getting started in the Transformational Cybersecurity Leader Triad depends on where you’re at in your career weighed against the current needs in the organization you are in. There’s no specific starting and ending point for your progression through the Triad.
Each course complements the other two and addresses any gaps in skills and knowledge the other courses might have. Some example approaches might look like this:
You’re at an entry point in your career with basic technical knowledge: The approach might be MGT512, MGT514, and then MGT521.
MGT512 builds up your technical and leadership skills, then MGT514 enables you to connect security with the business objectives, and finally MGT521 helps you lead change and steer the culture in the desired direction for security awareness.
You have a broad range of technical skills and want to make a transition to cybersecurity leadership: The approach might look like MGT514, MGT521, and then MGT512.
MGT514 and MGT521 provide the tools to start the transition process and then you can circle back and take MGT512 to further your technical knowledge.
You are in a security leadership position, have limited technical skills, want to drive security awareness, and lead change in the organization: The approach might be MGT512, MGT521, and MGT514.
MGT521 gives you the tools you need to build a security awareness program and steer change in the organization, MGT512 will provide you with base level knowledge you need from a technical perspective, and then MGT514 shows you how to build strategic plans for security and deliver on the security program.
Your path all comes down to what will benefit you the most and what your current skill set is. Regardless of where you start, the Transformational Cybersecurity Leader Triad gives you to tools you need to succeed build and deliver security programs in today’s modern organizations.
ABOUT THE AUTHOR
Joe Sullivan has over 20 years of experience in information security. Joe is Principal Consultant at Rural Sourcing in Oklahoma City where he manages and develops the security consulting services and the teams that provide them. Over his career Joe has worked in incident response, penetration testing, systems administration, network architecture, forensics, and is a private investigator specializing in computer crime investigations. Joe teaches MGT514: Security Strategic Planning, Policy, and Leadership. Read Joe's full profile here.


Joe Sullivan has over 20 years of experience in information security and is a senior security consultant for TrustedSec. Joe teaches LDR514: Security Strategic Planning, Policy, and Leadership.
Read more about Joe Sullivan