Tags:
This is Part 8 of a multi-blog series on the new NIS2 Directive. Explore the complete series:
Information sharing across the EU is essential to the new NIS2 Directive. However, according to Ciaran Martin, a leading global authority on cybersecurity, there may be some snags. Nevertheless, there are also lessons the EU can learn from the UK and US in this area.
Looking back at the history of cybersecurity and critical infrastructure in this century, it's remarkable how under-regulated vital sectors have been for cyber resilience for most of that period. There have been a few exceptions, like banking, where national regulations have been implicitly or even accidentally extended to cyber. However, before the first NIS directive, there was not much regulation for cyber.
Ciaran Martin is a leading global authority on cybersecurity who founded the UK's National Cyber Security Center and served as its first CEO. He currently holds the position of Professor of Practice at Oxford University's Blavatnik School of Government and is also a fellow at Herford College in Oxford. "Prior to NIS1, most of what we could do with critical infrastructure was to ask people nicely to improve their cybersecurity. And, in many respects, they responded to being asked nicely, but they didn't have to, and we knew they could cut corners or ignore us altogether. When the first NIS directive came in 2016, it helpfully set out a basic minimum framework of architecture and standards for critical sectors across the world."
NIS2 is expanding upon the previous framework with a broader definition and more comprehensive set of responsibilities for resilience. "The new directive is a direct requirement for all EU member states but applies to anybody wanting to do business in the EU," explains Martin. With this extraterritorial effect, NIS2 directly affects UK- or US-based organizations with EU operations. "Many of the key digital service providers in the European Union are headquartered in the United States, but they have huge operations in the EU, so they must comply with NIS2 and other European regulations. This directive is something people all over the world have to study."
The Challenge of Information Sharing
NIS2 aims to enhance information sharing across EU member states; however, Martin expects this to vary hugely across different EU nations. "I think it depends on the maturity of the model, too. Information sharing is a struggle to get off the ground in the UK. Some companies are reluctant to share, but there are also technical issues such as common formats," says the former NCSC CEO. "If you can't automate something, then it's just a bunch of words people can read. I think governments have to be capable of acquiring and sharing useful information and willing to do so because they get nervous about secrecy and confidentiality." He confesses that it will probably be easy to meet the letter of information sharing requirements; however, in terms of the spirit of that requirement and reaching a positive outcome helpful to companies, that is harder to achieve.
"Is it easy to set up a forum for information sharing that meets the requirements of NIS2? Yes. However, is it easy to establish a trusted ecosystem of useful information sharing on threats in which people have confidence? That is actually really, really hard. And very few industries or countries have done it well. In the end, the law isn’t magic."
Lessons the EU Can Learn from the US and UK
Martin says there are lessons to be learned like the importance of competent authorities, i.e., legal competence, skills, and ability. In his view, trusted government agencies, like the National Cyber Security Center, can play a convening role as neutral umpires among competitors. Another lesson is by investing in information sharing.
However, NIS2 doesn't require this of member states even though this is what is needed. Some in the cybersecurity community believe information sharing is the great disappointment of cyber defense over the last quarter century. Some even call it the hopes and prayers of cybersecurity. "Unfortunately, the NIS2 directive will not change that one way or the other. It will not do any harm or make things worse, but it will not fix the information sharing struggle that has been going on for so long. NIS2 fixes the gaps in the scope of NIS1, but what it doesn't do is magically fix difficulties found in cybersecurity cooperation. And it's not reasonable to expect it to."
Advice for Preparation
All member states must have the NIS2 Directive added to their national legislations by October 17th, 2024, leaving companies with just a few months to prepare. Martin is happy to share some advice for CISOs and leadership teams leading up to the new regulation:
- Know your obligations. The initial NIS1 Directive did not previously cover some industries, but it does now. Find out if your organization needs to comply, and if so, if your organization is important or essential and what obligations that entails.
- Get to know your national regulator. Building a personal relationship with the regulator so, in the case of an incident you know who you need to contact and report it to.
- Know your reasonable worst-case scenario. Look at what is most likely to go wrong that would trigger your NIS2 obligations. Model those scenarios, run simulations, and prepare for those eventualities.
- Know your defensive gaps. Find your organization’s real security defense gaps. One of the risks of NIS2 is making it strictly a compliance-based exercise. This works until it doesn’t, which is usually when something has gone wrong. In other words, NOS2 compliance will not prevent a breach, only knowing and addressing your security gaps will do that.
- Know and improve your organization’s resilience plan. Continually test and update your organization’s resilience plan, find the gaps, and address them.
5 Recommendations for Preparation
- Know your obligations
- Know your national regulator
- Know your reasonable worst-case scenario
- Know your defensive gaps
- Know and improve your resilience plan
Which Organizations are Essential or Important?
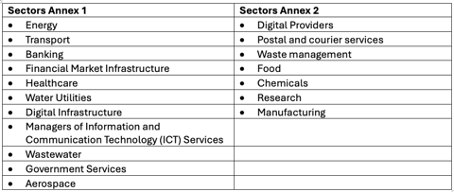
Essential entities: Large organizations operating in a sector from Annex 1 of the NIS2 Directive.
Key entities: Medium-sized organizations operating in an Annex 1 sector and medium and large organizations operating in an Annex 2 sector.
An organization is large based on the following criteria:
- a minimum of 250 employees, or
- an annual turnover of €50 million or more and a balance sheet total of €43 million or more.
An organization is medium-sized based on the following criteria:
- 50 or more employees, or
- an annual turnover and balance sheet total of €10 million or more.
In this series on NIS2, we highlight the new directive from different angles so that CISOs and their organizations can gain insight into how to deal with NIS2.
In the ever-evolving world of cybersecurity, staying compliant is key. With SANS, you have a partner in compliance, offering the latest courses and resources designed for NIS2 standards. Start navigating the compliance landscape today at www.sans.org/mlp/nis2.
As SANS maps out industry preparedness for the new EU Commission's NIS2 Directive, your insights are invaluable. Please take a moment to complete the NIS2 survey to contribute to our research. Your feedback will help us provide the guidance and resources needed for this and future directives.